Developers face a major security threat as over 100,000 repositories on GitHub are infected with malicious code.
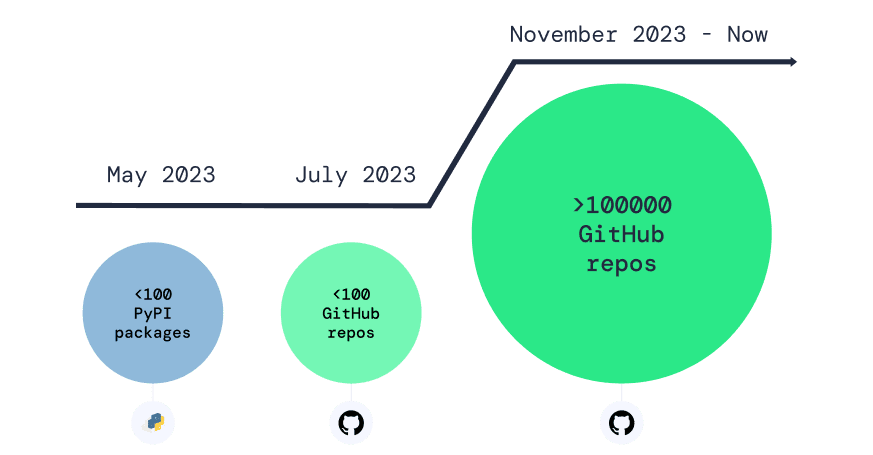
This resurgence of a malicious repo confusion campaign – detected by Apiiro’s security researchers – has impacted countless developers who unwittingly use repositories they believe to be trusted but are, in fact, compromised.
Similar to dependency confusion attacks – which exploit package managers – repo confusion attacks rely on human error, tricking developers into downloading malicious versions instead of legitimate ones.
Malicious actors clone existing repositories, infect them with malware loaders, upload them with identical names to GitHub, and then automatically fork them thousands of times—spreading them across the web through forums and other channels.
Once developers use these infected repos, the hidden payload unpacks layers of obfuscation—executing malicious Python code and binary executables. This modified code – often a version of BlackCap-Grabber – collects sensitive data such as login credentials and browser information, sending it to the attackers’ command-and-control server.
While GitHub swiftly removes most of the forked repos, automated detection misses many, allowing thousands to persist.
The removal process – which targets fork bombs – occurs within hours of upload, making it challenging to document the extent of the attack. The sheer volume of repositories involved in this campaign, combined with their automation, poses a significant challenge to detection and mitigation efforts.
This malicious campaign began in May 2023 with the spread of malicious packages on PyPI and highlights a broader trend of malware targeting software supply chains. As attention on package managers increases, attackers are shifting their focus to source control managers like GitHub.
(Photo by Roman Synkevych on Unsplash)
See also: Python packages caught using DLL sideloading to bypass security

Want to learn more about cybersecurity and the cloud from industry leaders? Check out Cyber Security & Cloud Expo taking place in Amsterdam, California, and London. The comprehensive event is co-located with other leading events including BlockX, Digital Transformation Week, IoT Tech Expo and AI & Big Data Expo.
Additionally, the upcoming Cloud Transformation Conference is a free virtual event for business and technology leaders to explore the evolving landscape of cloud transformation. Book your free virtual ticket to explore the practicalities and opportunities surrounding cloud adoption.
Explore other upcoming enterprise technology events and webinars powered by TechForge here.